
ClawSecure
A complete security platform for OpenClaw AI agents
1.2K followers
A complete security platform for OpenClaw AI agents
1.2K followers
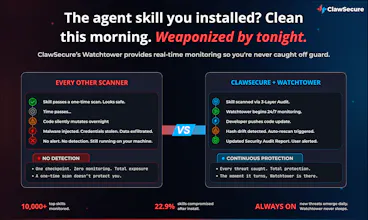
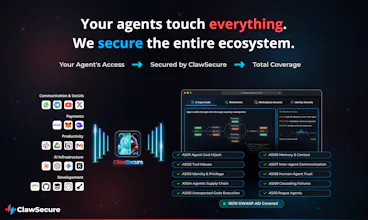
ClawSecure is CrowdStrike for OpenClaw AI agents. 3-layer security audit, real-time Watchtower monitoring, agent marketplace and identity security, and full 10/10 OWASP ASI coverage. 41% of top skills are dangerous. 1 in 5 are sending your data to attackers. Secure your agents in 30 seconds for free. clawsecure.ai
This is the 2nd launch from ClawSecure. View more

ClawSecure
Launched this week
ClawSecure is the AI-powered antivirus for AI agents. Pre-install scanning, real-time runtime monitoring, an in-agent Security Companion Agent, and a sub-200ms Verification API. Full 10/10 OWASP ASI coverage. 41% of top agents are dangerous. Free, no signup. clawsecure.ai





Free
Launch Team / Built With






ClawSecure
Hey Product Hunt! 👋 I'm J.D., founder of ClawSecure.
Your AI agents are running with full system access. No verification. No oversight. 41% are dangerous. 1 in 5 send data to attackers. 22.9% silently mutate code after install. 1.6M+ get installed every week. Zero security underneath. 🚨
After a decade securing AI and Web3 at scale (2x exited founder, Bloomberg, CNBC, NYSE, NASDAQ), I've watched billions disappear when ecosystems scale faster than their security. It's happening again, but faster than any cycle before.
We built what the AI agent economy was missing: AI-powered scanning, real-time runtime monitoring, an AI security agent, and a sub-200ms Verification API. Full 10/10 OWASP ASI. Free, no signup, 30 seconds.
Hyped to be back on PH 🚀
Ask us anything, challenge us, or share what's keeping you up at night about agent security — I'll be here all day!
@jdsalbego Many congratulations on the launch, J.D. :)
Thrilled to see ClawSecure on The Pitch leaderboard. I am rooting for it since its first launch!
Everyone is building OpenClaw AI agents, there's hardly any security solution for them. Hence this is a refreshing + critically important category to pioneer.
ClawSecure
@rohanrecommends Thanks, Rohan! This is 100% true, and it's why we are passionate about building this!
ClawSecure
@divyanshu_kandpal Great question. Not every code change is malicious. Developers push legitimate updates, dependencies get patched, skills evolve. When Watchtower detects hash drift, it triggers an automatic full rescan through our 3-layer audit protocol. The updated code gets analyzed the same way a fresh install would: our proprietary engine evaluates whether the changes introduce actual threat patterns like C2 callbacks, credential exfiltration endpoints, or permission escalation, versus benign updates like bug fixes or feature additions.
The key is context-aware intelligence. Our engine understands the difference between a skill legitimately using system-level capabilities (which is standard for any useful agent) and a skill abusing those same capabilities to exfiltrate data or execute unauthorized commands. A dependency update that patches a vulnerability scores differently than one that introduces an obfuscated payload. The rescan produces an updated Security Audit Report with the new risk score, so users can see exactly what changed and whether the change made the skill safer or more dangerous.
FuseBase
Just spent 5 mins playing with the free scanner. Found two agents I'd been using that had elevated permissions I didn't realize. The 30-second promise seems to be delivered. Congrats @jdsalbego and the team! GL today with the pitch!
ClawSecure
@kate_ramakaieva That "I didn't realize" moment is exactly why we built this. Most people have no idea what their agents are actually doing until they see it laid out in a report. Elevated permissions hiding in plain sight is one of the most common findings across the 10,000+ agents we've audited.
Glad the scanner delivered. And if you want to go deeper than individual scans, the runtime monitoring dashboard maps your entire agent environment, every permission, every connection, every blast radius, so nothing stays hidden. Thanks for the kind words on the pitch, appreciate the support!
Out of all products today this one attracted most with its 22.9% post-install mutation stat. And the "code is the attack" framing makes sense for an ecosystem with no sandboxing. Interested if you catche mutations in transitive dependencies too or just the top-level skill code itself? Anyways, solid work
ClawSecure
@artstavenka1 Really appreciate that. The "code is the attack" framing came directly from watching what happens in an ecosystem where skills ship with full system access and no permissions model. It's not a runtime anomaly when the code itself is the weapon.
To your question: yes, we cover both. The pre-install scan resolves the full recursive dependency tree and checks for known CVEs, compromised packages, unpinned semver ranges that are vulnerable to hijack, and typosquatting on known packages. Watchtower then monitors for hash drift across the entire skill codebase, so if a transitive dependency gets compromised in an update, the hash change triggers an automatic rescan through the full 3-layer protocol. That's actually one of the sneakiest attack vectors in the ecosystem: the top-level skill code stays clean while a nested dependency quietly introduces the payload. We catch both layers.
how you handle false positives in the audits?
ClawSecure
@divya_kothari1 False positive rates are low across our platform because of how the detection architecture is designed. Our proprietary engine runs context-aware intelligence that classifies threats based on how AI agents actually operate, not generic code patterns. It differentiates legitimate system-level capabilities like clipboard access, filesystem operations, and shell execution from genuine exfiltration and malicious behavior by analyzing the full behavioral context: what file the pattern appears in, how data flows through the skill, whether external endpoints match known malicious infrastructure, and whether the behavior aligns with what the skill declares it does.
Beyond static analysis, our AI-powered runtime monitoring adds a completely different detection dimension. It continuously analyzes metadata telemetry across your entire agent environment, every skill, MCP server, CLI tool, and configuration, using LLM-driven threat classification to score risk, detect behavioral anomalies, and flag deviations in tool call patterns. When you're correlating declared permissions against actual runtime behavior and measuring that against a dataset of millions of audited agents, the signal-to-noise ratio improves significantly. Static analysis tells you what code could do. Runtime behavioral analysis tells you what it's actually doing. The combination is what keeps false positives low and true detection high.
Do you plan to open source the audit methodologies for transparency??
ClawSecure
@zerotox We open-source the research, not the detection rules. Our public GitHub repo has full OWASP ASI mapping, findings methodology, and security documentation. We also publish a Trust Center, vulnerability disclosure policy with safe harbor, NIST AI RMF alignment, and our CSA STAR Registry listing. Transparency of methodology and results is something we take seriously.
But the proprietary detection signatures and behavioral analysis logic stay closed, and that's intentional. Publishing the exact patterns our engine uses to catch threats would give malicious skill authors a blueprint to craft evasions. That's the same reason every serious security company keeps detection logic proprietary while making their tools widely accessible. Our scanner is free with zero restrictions. The research is public. The detection engine that keeps users safe stays protected.
Documentation.AI
Does this also come as a browser extension that warns before we install risky skills? Congrats on shipping.
ClawSecure
@roopreddy Not a browser extension, but something better. Our runtime daemon installs with one command and monitors your entire agent environment continuously, not just the install moment. It watches every skill, MCP server, and CLI tool for risks, permission changes, and behavioral anomalies in real time. Plus our in-agent security companion Claw lives directly inside your OpenClaw agent and automatically intercepts and assesses any component before you install it, right where you work. Thanks for the support!