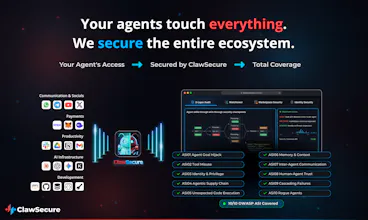
ClawSecure
The AI-Powered Antivirus for AI Agents
1.2K followers
The AI-Powered Antivirus for AI Agents
1.2K followers
ClawSecure is the AI-powered antivirus for AI agents. Pre-install scanning, real-time runtime monitoring, the first-ever AI CISO Security Agent, and a sub-200ms Verification API. Full 10/10 OWASP ASI coverage. 41% of agents are dangerous. Free, no signup. clawsecure.ai