
LeakScope — Supabase Security Auditor
Scan websites for exposed Supabase data and API leaks
5 followers
Scan websites for exposed Supabase data and API leaks
5 followers
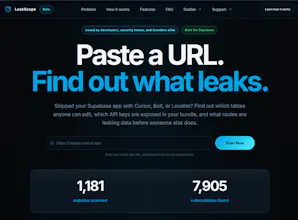
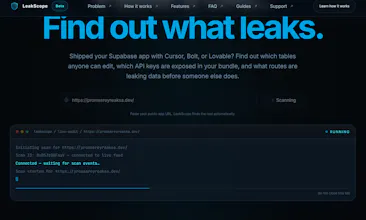
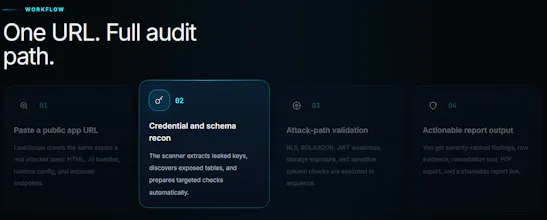
LeakScope scans live websites for Supabase data exposure and misconfigurations. Paste a URL and it checks for: • public Supabase tables • weak or misconfigured RLS policies • exposed API keys in JS • source maps in production • missing security headers The goal is simple: show what an anonymous user could access from the outside.


Quick update on LeakScope 👋
We just hit 1,000+ websites scanned. Genuinely didn't expect this kind of response so early — thank you to everyone who tried it and shared feedback. It means a lot.
Here's what's been added since launch:
🔍 Smarter crawling
LeakScope now detects your framework automatically — Next.js, Vite, CRA — and fetches the right chunks for each one. It was missing a lot of credentials before because they live in lazy-loaded chunks, not main.js. That's mostly fixed now.
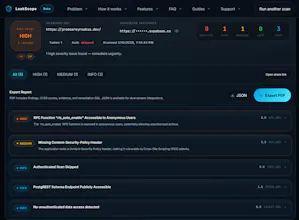
🛡️ Full CRUD testing
Previously we only tested SELECT on your tables. Now we test INSERT, UPDATE, and DELETE too — as both anonymous and authenticated users. A lot of apps that looked fine before are now showing critical issues.
🔐 More Supabase-specific checks
Added Vault secret exposure, Admin API probing, MFA enforcement checking, JWT role escalation, CDN transform bypass, database webhook SSRF risk, and row count oracle detection.
📄 Shareable reports
Every scan now generates a unique report URL that's valid for 48 hours. Send it to your team or your client.
🤖 AI analysis
Optional AI layer that writes plain English remediation guidance for each finding — built for developers who don't speak security.
Still a lot more coming. If you hit any issues or have ideas, drop them in the comments — we read everything.
https://www.leakscope.tech/
We updated the core black-box scanner last week — better detection for common Supabase leaks in JS bundles and more accurate probing for weak RLS patterns. Stats now at 1,623 sites scanned and 11,760 vulns found (still seeing the same recurring stuff in vibe-coded apps).
And now we're deep in the next phase:
Building deeper scans that let you optionally authorize your Supabase project for internal checks without exposing anything extra.
Working on scheduled/continuous monitoring — auto weekly scans + simple alerts if new issues pop up.
Starting the CLI prototype — aiming for easy local/CI use like leakscope scan <url> or bulk mode.
It's all still early, but feels good seeing real patterns from scans inform the direction.
What do you think we should push harder on first? Deeper auth scans? Monitoring setup? CLI basics? Or something we're missing?
If you've run a scan lately, reply with any surprises (keep it anonymized) — helps a ton.
Thanks for the early eyes! https://www.leakscope.tech/