Golf
Enterprise MCP Control Plane
732 followers
Enterprise MCP Control Plane
732 followers
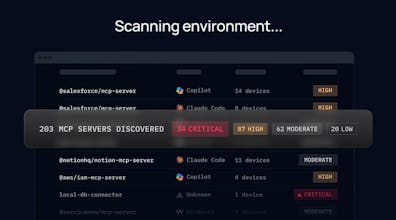
Golf is the enterprise control plane for MCP. It gives security and IT teams full visibility into how AI connects to enterprise systems — with policy enforcement, real-time threat blocking, and a complete audit trail. Discover, enforce, audit. End-to-end.