Launching today

buildcage
Restrict outbound access in Docker builds on GitHub Actions
1 follower
Restrict outbound access in Docker builds on GitHub Actions
1 follower
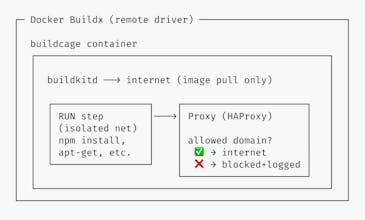
Docker builds can fetch from any server on the internet. A compromised dependency could silently exfiltrate your build secrets. buildcage prevents this. Define allowed domains, and everything else is blocked. Your Dockerfiles stay the same — no proxy injection, no certificate changes. TLS is never intercepted. Drop-in builder for Docker Buildx and GitHub Actions. - Audit mode to discover dependencies - Restrict mode to enforce your allowlist - Self-hostable for full control Open source.


Hello Hunters,
I built buildcage to solve a problem we kept running into at work: when you run npm install in a Dockerfile, that command can connect to anywhere on the internet, with no visibility into where it goes. A compromised package could exfiltrate build secrets or phone home to an attacker's server.
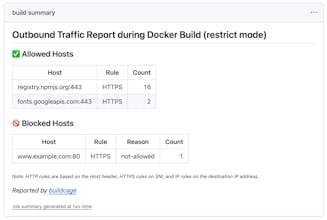
buildcage restricts outbound network access during Docker builds. Define allowed domains, and everything else is blocked and logged. Your Dockerfiles stay exactly the same.
This is not a silver bullet. If a malicious package comes through a legitimate registry, buildcage can't catch it. The way I think about it: buildcage is a last line of defense. If something slips through all your other measures, at least it can't call home to an attacker's server.
The project is fully open source. You can fork it into your own GitHub org and build the image yourself — for a security tool, I think that matters.
I'd love to hear your thoughts — whether it's about the approach, the limitations, or how this fits into your own workflow!