
Aegis
Your AI agent's API keys, locked down and audited
2 followers
Your AI agent's API keys, locked down and audited
2 followers
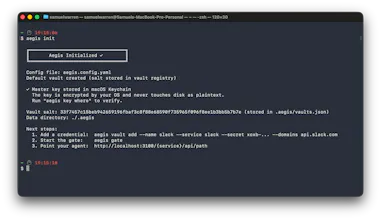
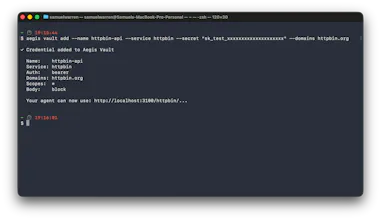
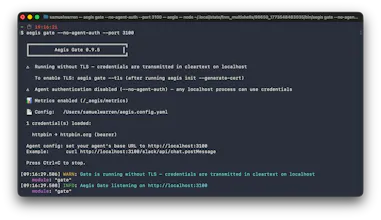
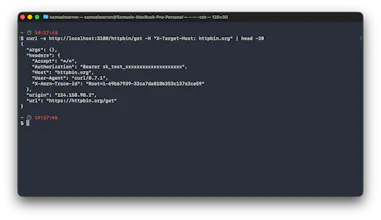
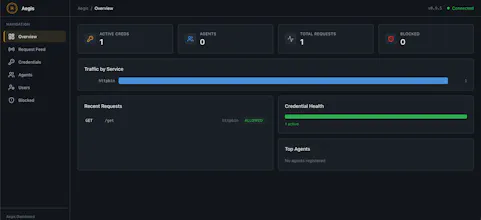
Local-first proxy that keeps API keys out of AI agent context. Your agent sends requests to localhost — Aegis injects real credentials on the outbound HTTPS request. The agent never sees the raw key. Encrypted vault, domain allowlists, full audit trail, per-agent scoping, YAML policy engine, and native MCP server for Claude Desktop, Cursor, VS Code, Windsurf, and Cline. No SDK. No cloud. No code changes. Open source (Apache 2.0).


Hey 👋 I'm Sam, the maker. I built Aegis because AI agents need to call real APIs — Slack, GitHub, Stripe — and the standard way to give them access is handing over the raw API key. Drop it in an env var, paste it into a config file, and hope for the best.
The problem is that agents process untrusted input: user prompts, tool outputs, web content. A prompt injection can instruct the agent to exfiltrate any credential it can access. Even without an attack, there's no domain restriction (your Slack token can be sent anywhere) and no audit trail (you can't see what the agent did).
I wanted a simple rule: the agent should never see the real key.
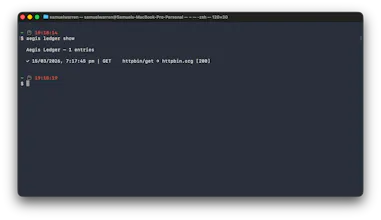
How it works: Your agent sends requests to `localhost:3100/slack/...` and Aegis injects the real Bearer token on the outbound HTTPS request. It checks the target domain against an allowlist (your Slack token can only reach slack.com), and logs every request. The agent gets the API response, but never the credential.
It's also a native MCP server, so Claude Desktop, Cursor, VS Code, Windsurf, and Cline can use it directly — no SDK, no framework coupling, no code changes.
What's under the hood:
- TypeScript + Node.js, single CLI binary
- SQLite encrypted at rest (AES-256-GCM + ChaCha20-Poly1305)
- Master key stored in OS keychain (macOS Keychain / Windows Credential Manager / Linux Secret Service)
- Published STRIDE threat model (28 threats, 0 critical/high unmitigated)
- YAML policy engine for teams (method, path, rate limit, time window restrictions)
- 820+ tests across every module
- Apache 2.0, runs entirely on your machine
Try it in 60 seconds:
Your agent hits localhost:3100 - credential injected, domain-checked, logged.
Happy to answer any questions about the architecture, security model, or use cases. Full source, threat model, and security architecture docs are in the repo.
GitHub: https://github.com/getaegis/aegis
Docs: https://github.com/getaegis/aegi...